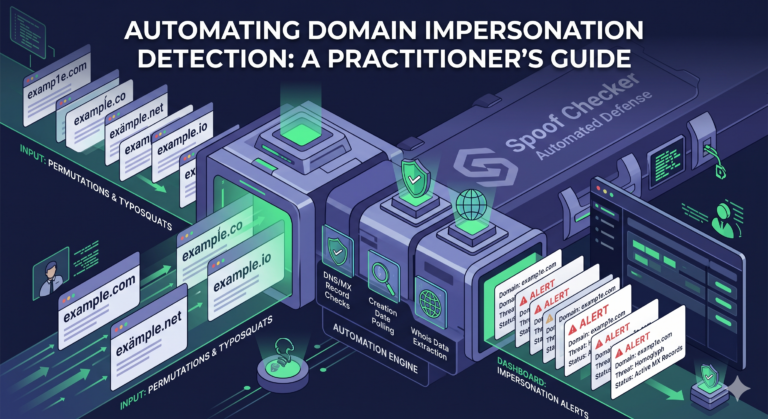
Automating Domain Impersonation Detection
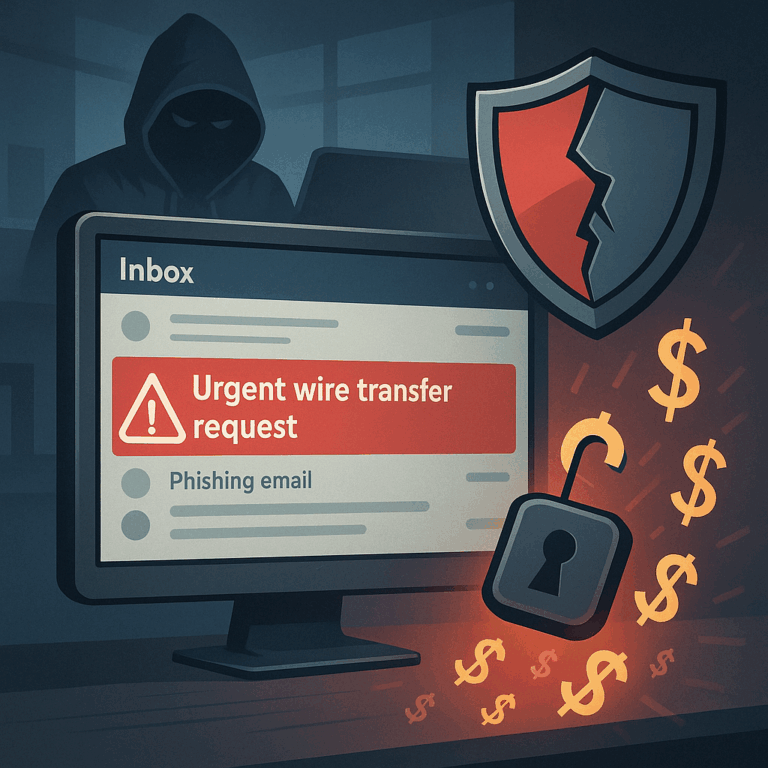
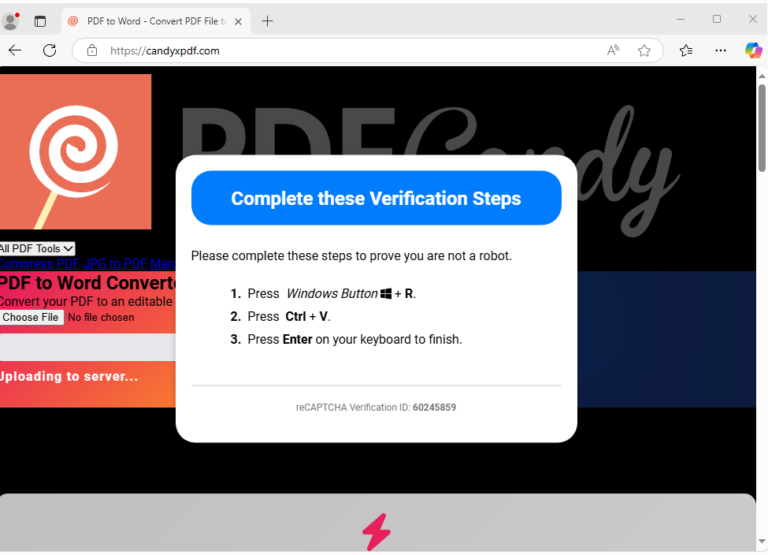
Automating Domain Impersonation Detection: Building and Scaling a Lookalike Domain Pipeline Table of Contents Why Waiting Is Not a Defense Strategy Step 1: Generating the Permutation Matrix Step 2: Automating DNS and WHOIS Validation Step 3: Integrating with the Security Stack Why Scripts Fail at Scale From Scripts to Automated Domain Impersonation Detection Why Waiting…