Automating Domain Impersonation Detection
Automating Domain Impersonation Detection: Building and Scaling a Lookalike Domain Pipeline
Table of Contents
Why Waiting Is Not a Defense Strategy
Waiting for a user to report a suspicious email is not a domain defense strategy — it is an incident response trigger. By the time a lookalike domain hits an inbox, the infrastructure has already been registered, weaponized, and deployed.
For security operations teams and MSPs managing multiple attack surfaces, the only way to get left of boom is to operationalize domain impersonation detection before threats reach the inbox. According to the FBI’s Internet Crime Complaint Center, Business Email Compromise attacks — the primary payload delivered through lookalike domain infrastructure — cost organizations $2.9 billion in 2023 alone. You need to know when a threat actor registers a homograph or typosquat of your primary domains before they configure the MX records to send mail.
Below is the technical breakdown of how to build an automated detection pipeline — and why scaling it requires more than just a Python script.

Step 1: Generating the Permutation Matrix
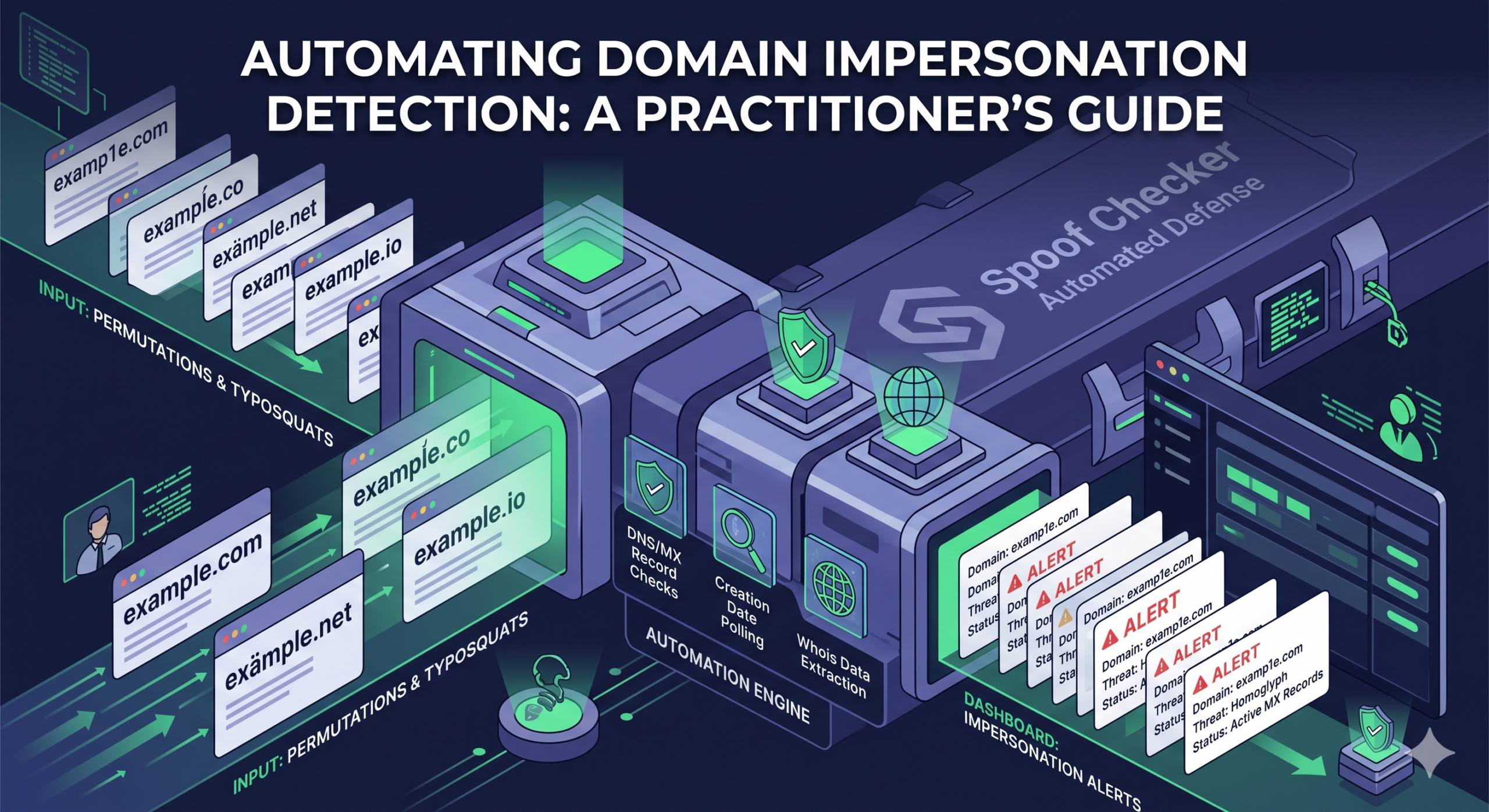
The first phase of automation is mapping every possible way an attacker could spoof your domain. This goes far beyond simple typos. A robust domain impersonation detection engine must programmatically construct hundreds — sometimes thousands — of variants for each protected domain.
Your detection script or platform needs to account for the following permutation classes:
exmple.com or exampple.com. These variants exploit fast typing and visual skimming in email clients.
exomple.com. Simple to generate at scale, and surprisingly effective against users who skim links rather than reading them character by character.
exmaple.com. Adjacent-key transpositions are statistically predictable from standard keyboard layout analysis and straightforward to enumerate programmatically.
.com for .net, .co, .io, or country-code TLDs like .cm (Cameroon) — which routinely intercept fat-fingered .com traffic without any active deception required.
Step 2: Automating DNS and WHOIS Validation
Generating a list of 5,000 potential lookalike domains is useless in isolation. The core of the pipeline must actively query global DNS infrastructure to determine which domains exist — and critically, what they are configured to do.
Step 3: Integrating with the Security Stack
Once the pipeline identifies a live threat, the data must move immediately into the existing workflow. Manual handoffs introduce delay — and at this stage, every minute of delay is a window for the attack to progress.
The output of the detection engine should be formatted as JSON or CEF to pipe directly into your SIEM or ticketing system. From there, analysts can initiate takedown requests with the registrar or preemptively block the lookalike domain at the Secure Email Gateway (SEG) and firewall levels before any mail is delivered to end users.
Why Scripts Fail at Scale
Building a Python script to run this domain impersonation detection pipeline for a single domain is a solid weekend project. Running it reliably across dozens of client environments is an operational nightmare. When MSPs or lean security teams try to scale homegrown detection scripts, they consistently hit three critical walls — and according to the Anti-Phishing Working Group, the volume of new lookalike domain registrations continues to grow year over year:
API Rate Limiting
High-volume DNS and WHOIS lookups will quickly get your IPs blacklisted or throttled by public resolvers. At scale, this is not a minor inconvenience — it creates blind spots in detection coverage that threat actors can exploit.
State Management
An automated system must remember what it found yesterday. Alerting every day on the same parked domain is noise. The signal is when that parked domain suddenly adds an MX record. Managing this delta-tracking requires a dedicated database — not a script.
Multi-Tenant Complexity
Hardcoding client domains into a script does not scale. MSPs need a centralized dashboard to add, remove, and isolate domains by client environment without touching code for every configuration change.
| Challenge | DIY Script | Purpose-Built Platform |
|---|---|---|
| DNS/WHOIS Rate Limiting | IP blocks and throttling from public resolvers; detection gaps at volume | Distributed infrastructure and rotated IPs; no throttling risk at scale |
| State Management | Requires building and maintaining a custom database and delta-tracking logic | Built-in change tracking; alerts fire only on meaningful state changes |
| Multi-Tenant Complexity | Hardcoded domains; no client isolation; code changes required per update | Centralized dashboard; add, remove, and isolate domains per client instantly |
| Alert Fidelity | Raw results with no context-aware scoring; analysts manually filter noise | Risk-scored alerts enriched with WHOIS age, MX status, and TLS signals |
From Scripts to Automated Domain Impersonation Detection
If your team is spending hours maintaining custom detection scripts — or navigating legacy enterprise platforms that hide their tooling behind aggressive sales cycles — you are consuming response capacity that should be directed at actual threats.
Detection should be frictionless. A production-grade platform handles the permutation logic, manages the lookup state, and pushes high-fidelity alerts the moment a threat actor configures a DNS record on a lookalike domain. Spoof Checker is built for exactly this — giving IT teams and MSPs transparent, self-serve typosquat monitoring with no infrastructure to build or maintain.
Key Takeaways
- Detection after a user reports a suspicious email is incident response, not prevention. The pipeline must surface threats before MX records are configured and mail is sent.
- A single protected domain can generate 5,000+ lookalike variants. Only automated DNS querying can determine which are registered and actively resolving.
- MX record presence on a lookalike domain is the definitive signal of an imminent BEC threat — it must be validated immediately and automatically, not manually.
- WHOIS creation date is a primary severity signal: a lookalike domain registered within 48 hours demands immediate escalation.
- DIY scripts fail at production scale on three fronts: DNS/WHOIS rate limiting, state management, and multi-tenant complexity.
- A production-grade pipeline requires distributed DNS infrastructure, built-in delta tracking, and SIEM/SOAR integration from day one.
Start Monitoring Your Domains — Free
Spoof Checker continuously scans for typosquats, homoglyphs, and lookalike domains registered against your brand. No scripts to write. No infrastructure to maintain.
Sign Up Free